How to Prevent the 3AM Client Crisis: Operational Mastery for Ultra-Luxury Concierge Scheduling
When a credentialed specialist calls out hours before a VIP arrival, static shift plans collapse. Learn how credential-based scheduling protocols reduce emergency substitution time from 45 minutes to under 15—protecting client trust and operational reputation.
The 3AM Credential Crisis
It is 03:00 AM. A Tier-1 CEO is touching down in Beijing for an unscheduled diplomatic meeting. Your roster shows a Mandarin-speaking concierge with active diplomatic clearance assigned to the arrival. Then the text comes in: a family emergency. The specialist is offline.
The shift lead opens the static schedule. They see twenty other names, but the spreadsheet doesn't show who has the specific "Vatican Protocol" certification or who holds a current "Liaison Alpha" clearance for the Beijing district. The search for a replacement begins with a frantic "beg the team" phone tree. By 03:45 AM, the CEO is at the curb with no one to meet them. The $50k annual retainer isn't just at risk; the firm's reputation for "invisible perfection" is shattered.
In ultra-luxury operations, a "covered shift" is meaningless if the person standing there lacks the specific cultural, linguistic, or security credentials the client requires. This is the gap that most scheduling software was never built to close. Your clients don't pay for warm bodies—they pay for verified expertise delivered without friction, regardless of the hour.
Why Static Shift Plans Collapse Under VIP Unpredictability
Legacy tools like Deputy or Shiftbase are designed for high-volume, low-variability environments where one "server" or "clerk" is functionally equivalent to another. In luxury concierge operations, your "inventory" is actually a matrix of highly specific human capital.
Gap 1: Spreadsheets can't track multi-layered credentials. A static roster shows names and hours. It does not show that Maria speaks Mandarin Level 5 and holds diplomatic clearance and has successfully managed three prior interactions with this specific client. When the 3AM callout happens, you're scrolling through a phone list trying to remember who has what.
Gap 2: Fixed rosters assume predictable demand. Ultra-high-net-worth clients operate on 2-to-6-hour notice windows. A Paris itinerary becomes a same-day Vatican private tour requiring Italian fluency and Catholic protocol expertise. Your rostered concierge has neither credential, and the shift starts in four hours. Static plans cannot respond to this velocity.
Gap 3: Manual substitution takes 45-90 minutes. VIP expectations allow under 15 minutes. Every minute spent on a phone tree is a minute the client waits. When you finally find someone, you're not confident they're the right someone—you're just relieved they answered.
Tools like Deputy and Shiftbase handle shift coverage well, but lack the real-time credential verification and client preference mapping that ultra-luxury concierge operations require when a specialist calls out hours before a VIP arrival.
The Credential-Gap Shield Approach
To move beyond "finger-crossed" scheduling, operations directors must implement the Credential-Gap Shield. This methodology treats every shift not as a block of time, but as a set of requirements. By digitizing specific credentials (e.g., "Mandarin Level 5," "Yacht Access Verified," "UHNW Relationship History"), the system creates a protective layer.
When a callout occurs, the 15-Minute Pivot protocol kicks in. Instead of searching a phone book, the manager sees a filtered pool of available staff who already meet the client's specific "Tier 1" requirements. This isn't just about who is awake; it's about who is capable. The goal is to move from a reactive "who can cover this?" to a proactive "who is the perfect match?" in seconds.
The framework operates on three pillars:
- Pre-validated credential pools: Every concierge's certifications, language scores, cultural training, and security clearances are digitized and kept current.
- Client preference mapping: Each VIP client profile lists mandatory and preferred credentials—no guesswork during emergencies.
- Automated filtering: When a callout triggers an alert, the system immediately highlights only those staff who meet all mandatory criteria and are available within the required time window.
This transforms your emergency response from a manual search into a selection process. You're not hunting for a needle in a haystack; you're choosing from a curated set of qualified candidates who already passed the filter.
Step-by-Step: Building a 15-Minute Pivot Protocol for Ultra-Luxury Concierge
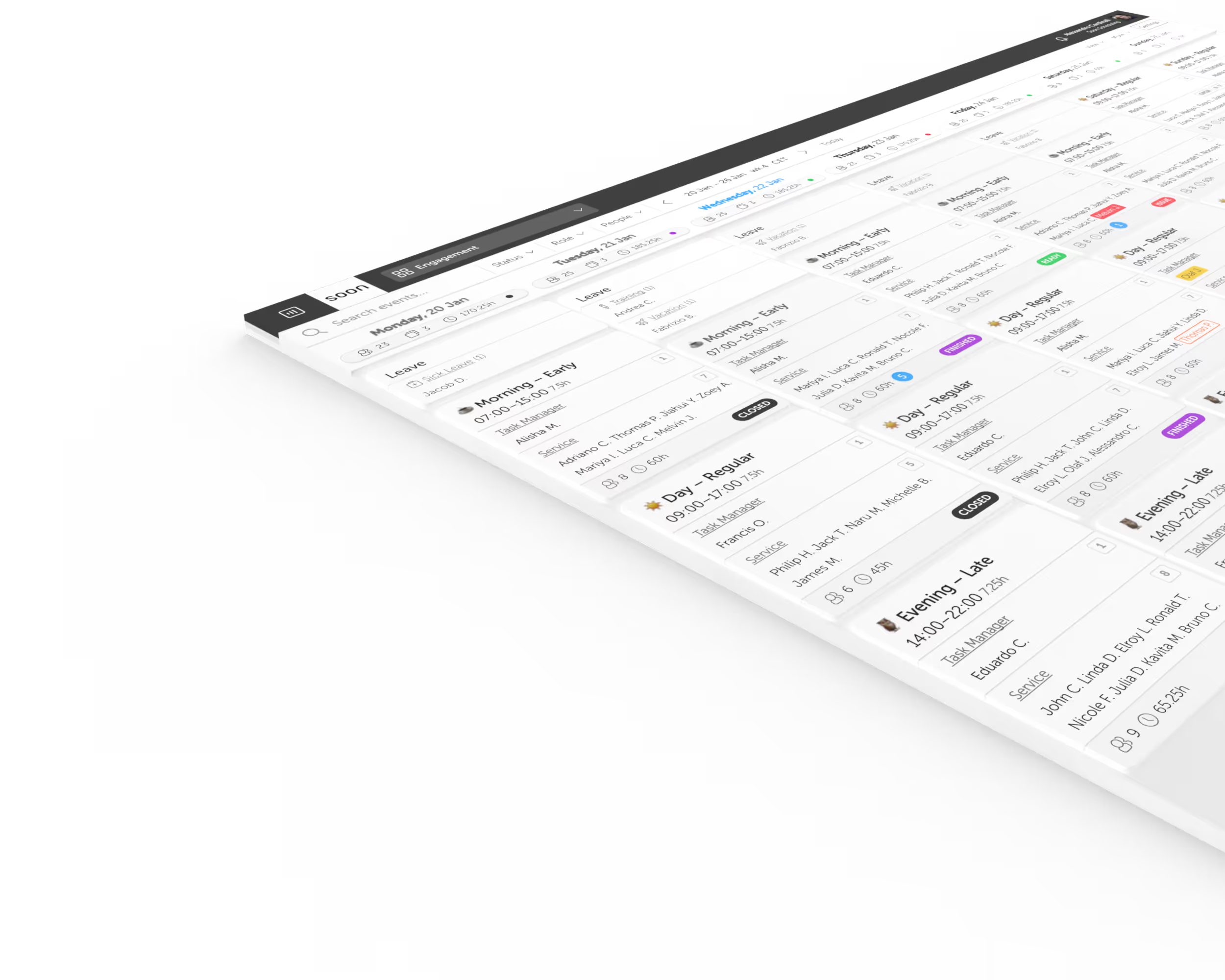
Step 1: Audit and digitize all concierge credentials. Move beyond the HR file. Create a digital matrix of every concierge's language scores (e.g., "Mandarin HSK 5," "Italian CILS B2"), cultural certifications (e.g., "Vatican Protocol Certified," "Middle East Business Etiquette"), access clearances (e.g., "Yacht Access Monaco," "Diplomatic Liaison Beijing"), and client relationship logs (number of successful interactions per VIP client). In Soon, these are categorized by roles and skills to ensure they are searchable in real-time.
Step 2: Map credentials to client preference tiers. Not all clients have the same requirements. Tier your clients based on service complexity. A "Tier 1" client may require a concierge with at least three prior successful interactions, specific language certifications, and active security clearances. A "Tier 2" client may only require language and cultural fluency. Document these mappings so that every shift is attached to a specific client profile with clear credential requirements.
Step 3: Create credential-based backup pools with 24/7 availability windows. Identify which staff members meet the criteria for each client tier and confirm their availability windows. This isn't about who can work nights—it's about who is qualified and available to cover a Tier 1 client at 3AM. Build these pools before the crisis, not during.
Step 4: Set up automated alert triggers for callouts less than 6 hours before shift start. When a specialist calls out within this critical window, the system should instantly send alerts to the pre-filtered backup pool. Use mobile-first notifications (SMS, push) to ensure immediate visibility. The alert should include the client profile, required credentials, and shift details.
Step 5: Implement The 15-Minute Pivot—automated matching plus SMS confirmation loop. The system sends the alert only to qualified backups. The first responder who confirms gets the assignment. If no one responds within 5 minutes, the system escalates to the next tier of qualified staff or alerts the operations director. This closed-loop communication eliminates the phone tree and ensures accountability.
Step 6: Build post-incident review protocols. After every intraday change, review the "who" and "why." If a credential mismatch occurred, update the client's profile immediately to prevent a second failure. If a qualified backup was unavailable, assess whether additional training or hiring is needed.
Real example walkthrough: Resolving the Vatican tour scenario in 12 minutes. A family office client changes a Paris itinerary to include a same-day Vatican private tour requiring Italian fluency and Catholic protocol expertise. The rostered concierge has neither credential, and the shift starts in 4 hours. The operations manager triggers the 15-Minute Pivot. The system filters the team to show three available concierges who hold "Italian CILS B2" and "Vatican Protocol Certified" credentials. An SMS alert is sent at 11:02 AM. The first qualified concierge confirms at 11:08 AM. By 11:14 AM, the client profile is updated, the new concierge is briefed, and the shift is reassigned. The client never knows a substitution occurred.
The Ripple Effect: What Happens When Credential Matching Fails
The cost of a scheduling mismatch in luxury services is rarely just a missed shift; it is a cascading operational failure.
Client outcome: Loss of $50K+ annual retainer after a single credential mismatch. When a VIP experiences a service failure—a concierge who doesn't speak the required language, lacks cultural awareness, or has no prior relationship history—they don't complain. They leave. In ultra-high-net-worth networks, word-of-mouth damage spreads faster than you can recover.
Staff outcome: Burnout from emergency "beg the team" phone trees at 2AM. When you don't have a Credential-Gap Shield, you rely on the same three "reliable" people for every emergency. These top performers receive frantic calls at all hours, leading to exhaustion and eventual turnover. Losing a highly credentialed concierge costs far more than the hire—it's the loss of client relationships and institutional knowledge.
Operational outcome: Inability to scale luxury service offerings beyond 20-30 active clients. Without automated credential matching, every new client adds exponential complexity to your manual substitution process. Operations directors become bottlenecks, unable to delegate emergency decision-making because only they hold the mental map of who has what credential.
Compliance and reputational outcome: If you cannot prove why a specific concierge was assigned to a sensitive client (e.g., diplomatic itinerary, cross-border travel), you face compliance risks and audit failures. In regulated environments or when handling clients with security protocols, documentation of credential matching is not optional—it's a legal and operational requirement.
Operationally, manual "phone tree" recovery costs a shift lead an average of 45-90 minutes per incident—time that should be spent on client intelligence and proactive service design, not firefighting.
Getting Started with Credential-First Concierge Scheduling
Most concierge operations are currently running on a mix of WhatsApp, Excel, and hope. You can begin professionalizing your response today by performing a Credential Audit. List your top five most frequent VIP requirements (e.g., "Mandarin + Diplomatic Clearance," "Italian + Vatican Protocol," "French + Yacht Access"). Cross-reference them with your current roster. If you can't identify three qualified backups for each requirement in under five minutes, your operation is at risk.
Immediate action: Audit your credential tracking system today. If it lives in spreadsheets, HR files, or people's heads, it's not operational intelligence—it's tribal knowledge waiting to walk out the door.
30-day goal: Digitize all concierge certifications and client preference data. Build a single source of truth that maps every staff member's credentials to the specific client requirements they can fulfill.
90-day goal: Implement automated credential-matching for backup staffing. Move from manual phone trees to filtered, automated alerts that reach only qualified backups within seconds of a callout.
Modernizing this workflow doesn't require an enterprise overhaul. Soon provides the tools to build these protocols naturally, with a Team plan starting at €8 per user/month (billed annually) or €10 monthly, and a Business plan at €16 per user/month (billed annually) or €20 monthly for more advanced constraint-based needs and optimization objectives that prevent "hero burnout" by balancing workload across your credentialed pool.
Frame this investment not as software cost, but as insurance against the operational and reputational cost of credential mismatches. A single failed VIP interaction costs more than a year of scheduling infrastructure.
You can explore the full feature set and detailed plan comparisons at soon.works/pricing. Start building your Credential-Gap Shield today to ensure your 3AM crisis never reaches the client's ears. Book a demo or explore the platform at soon.works.